Give your business a competitive edge
-
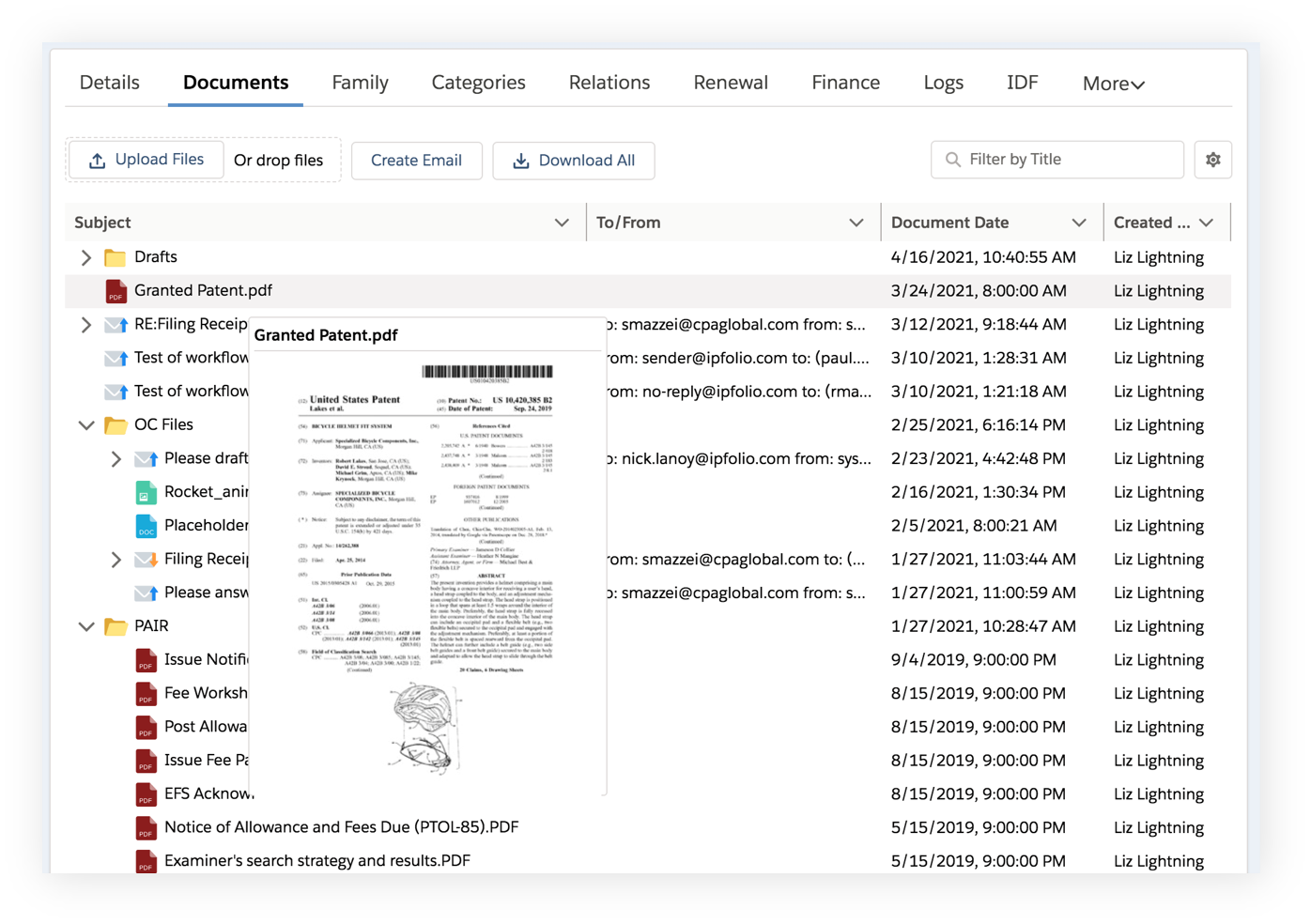
Maximize operational efficiency
Empower busy IP teams to keep up with increasing filing and data volumes. Save time and money by eliminating manual tasks such as data entry and repetitive steps through workflow and process automation. -
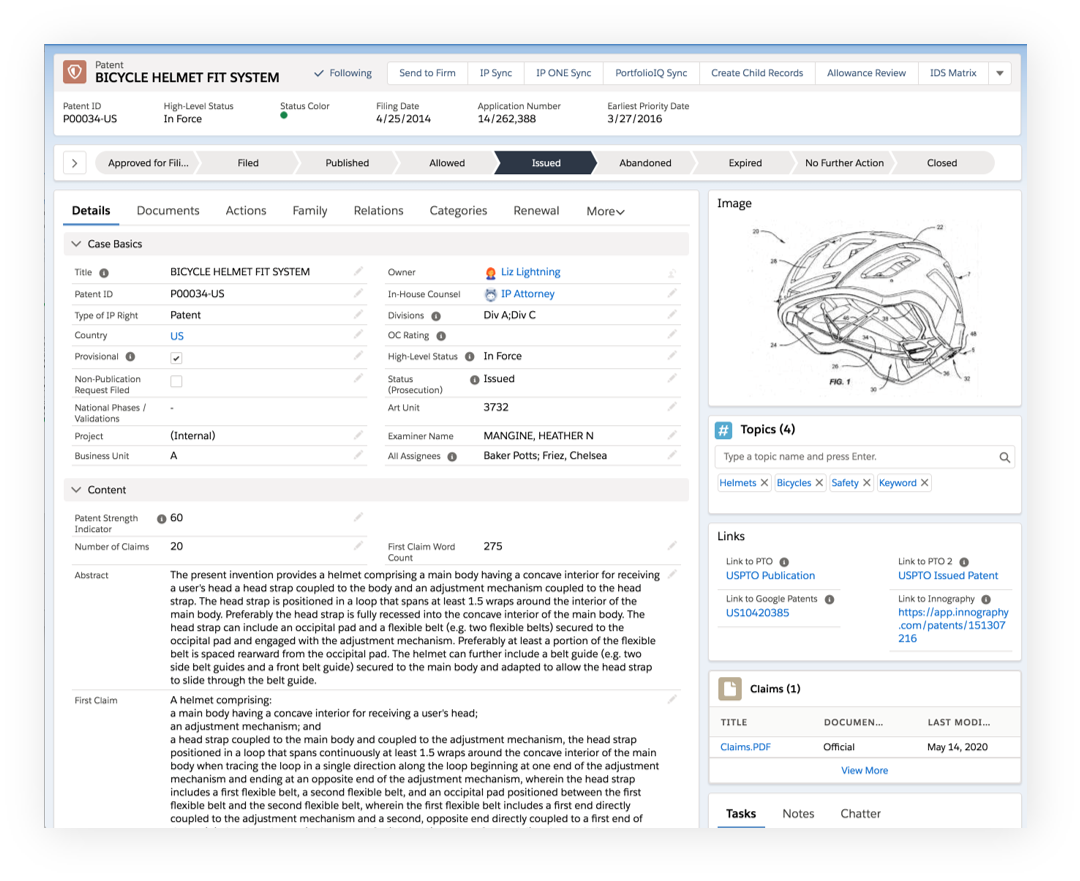
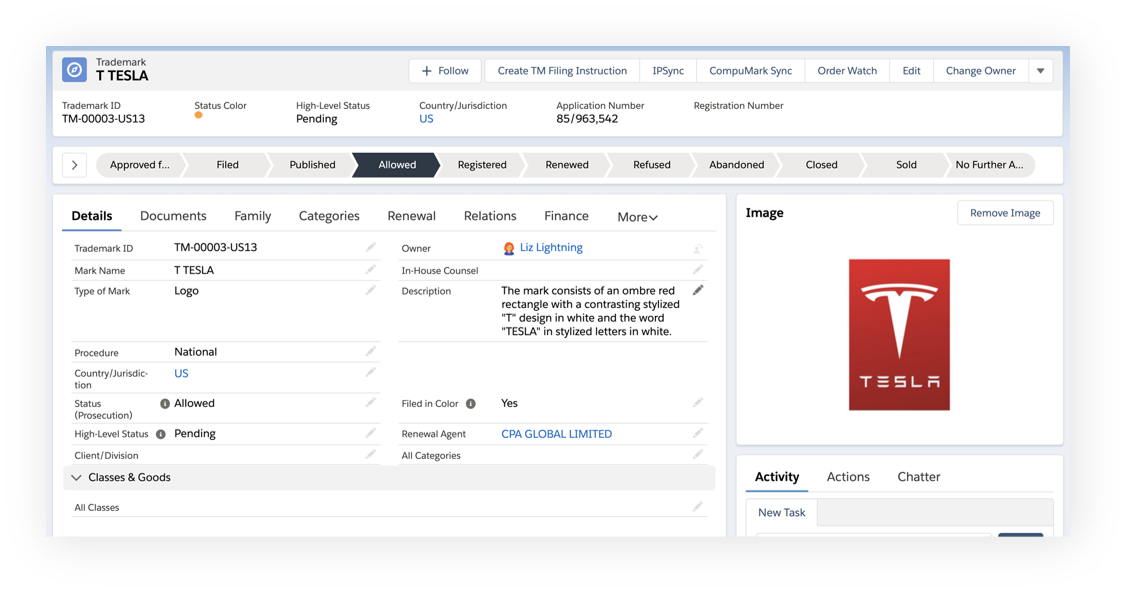
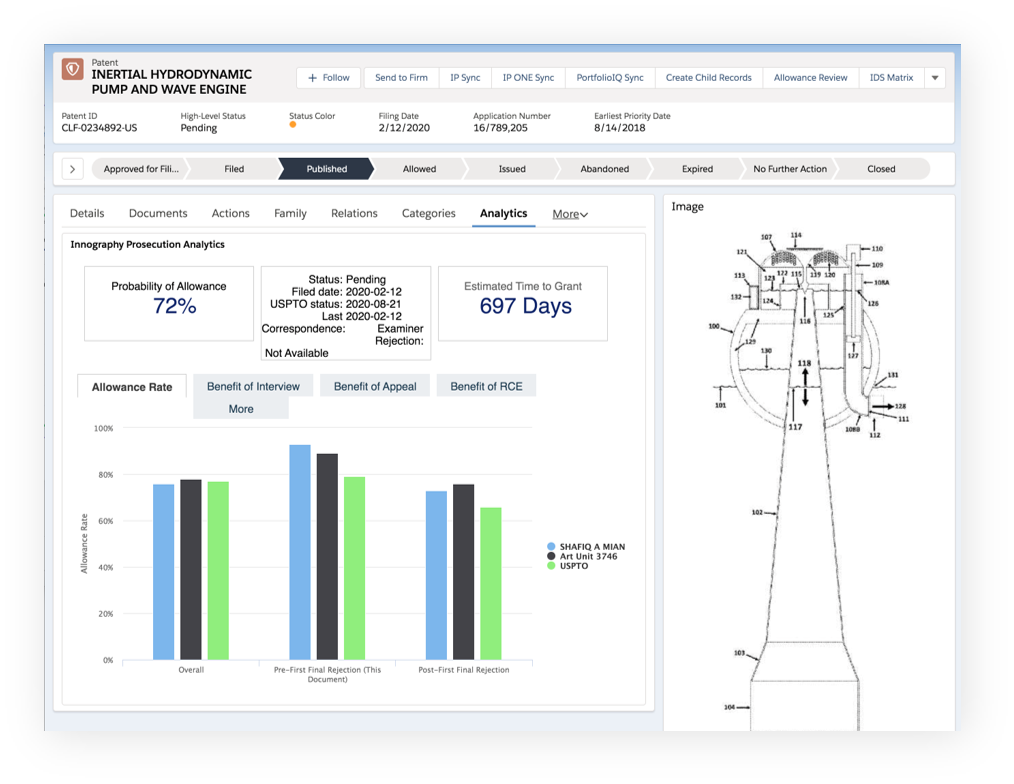
Get actionable insights
Plan and act strategically with analytical insights based on clean, reliable data that enable more informed IP decisions. Easy access to Clarivate IP data helps provide a single source of truth across your IP lifecycle. -
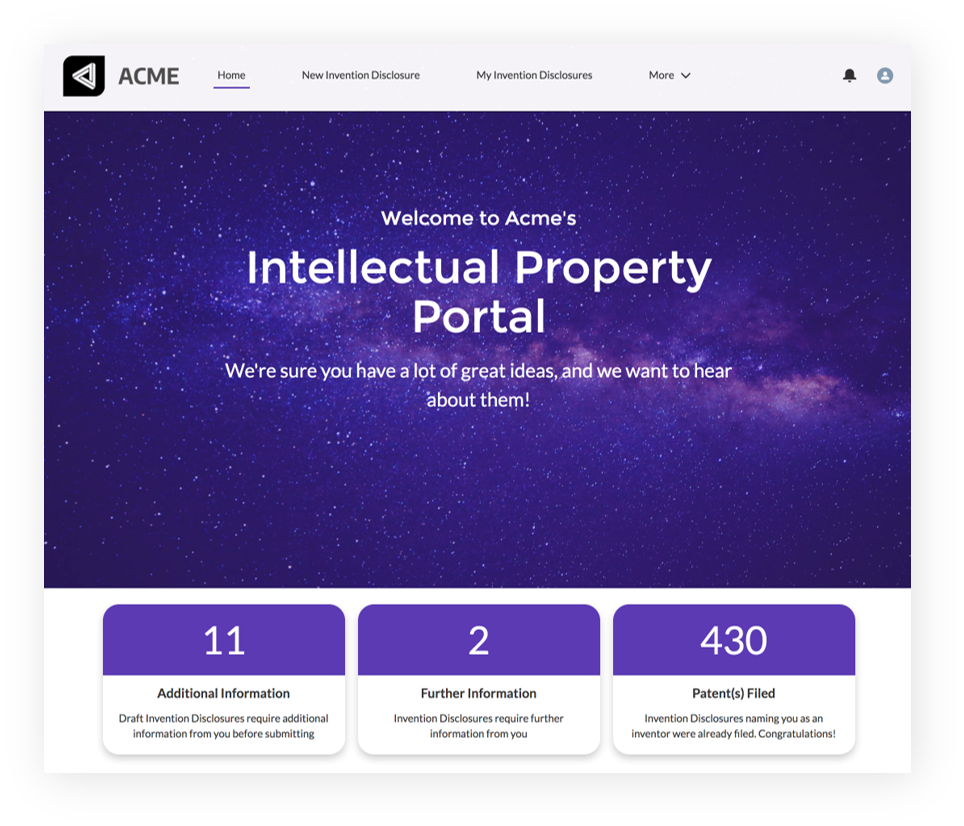
Improve collaboration
Connect your IP ecosystem with IPfolio. Collaborate and interact seamlessly with inventors, outside counsel, and other stakeholders from any device in a connected IP ecosystem.